 It is our responsibility at Emory to be aware of the security threats to our IT environment and to take reasonable and appropriate steps to protect against these threats. As Emory’s Chief Information Security Officer, I would like to share with you an overview of the importance of protecting your data and your access to our network.
It is our responsibility at Emory to be aware of the security threats to our IT environment and to take reasonable and appropriate steps to protect against these threats. As Emory’s Chief Information Security Officer, I would like to share with you an overview of the importance of protecting your data and your access to our network.
Cyber Threat Landscape
At a macro level, we need to be aware that we are dealing with threat actors that are not just kids in their mom’s basements. They are often organized, sophisticated, and highly motivated. The overwhelming number of threats today are driven by the promise of financial gain, either through ransomware, theft of intellectual property, or identity theft.
 There are also nation-state actors with very advanced capabilities that are interested in a broad array of information that you wouldn’t necessarily think is important until you realize their desires go well beyond stealing the latest military technology or state secrets. Many of these actors are looking to obtain unfair advantages in business negotiations, competitive bidding scenarios, or bringing new and innovative products to market, and top tier research institutions like Emory are prime targets for such actors.
There are also nation-state actors with very advanced capabilities that are interested in a broad array of information that you wouldn’t necessarily think is important until you realize their desires go well beyond stealing the latest military technology or state secrets. Many of these actors are looking to obtain unfair advantages in business negotiations, competitive bidding scenarios, or bringing new and innovative products to market, and top tier research institutions like Emory are prime targets for such actors.
We are also beginning to see a lot of cyber threat activity directed at exploiting the Internet of Things. The “things” are all the devices, big and small, that are nonetheless connected to the Internet, such as video cameras, home internet routers, smart televisions and video players. Do you think about updating the firmware in a wireless light fixture in your house? Hundreds of millions of devices are vulnerable and exploitable. Earlier this year, there was a large-scale denial-of-service attack that leveraged hundreds of thousands of compromised private home routers in the attack. In the next couple of years, the number of these devices connected to the internet will be in the billions.
 We have also seen the rise of advanced ransomware threats, where actors will access your most sensitive data, encrypt it, and then demand an exorbitant ransom get your access back. Hollywood Presbyterian Medical Center, in California, recently paid a $17,000 ransom in bitcoin to regain access to their patient data. Our own city of Atlanta had its systems ransomed for $51,000, did not respond to attackers’ demands fast enough, and will ultimately spend more than $11.5 million to recover from the data loss.
We have also seen the rise of advanced ransomware threats, where actors will access your most sensitive data, encrypt it, and then demand an exorbitant ransom get your access back. Hollywood Presbyterian Medical Center, in California, recently paid a $17,000 ransom in bitcoin to regain access to their patient data. Our own city of Atlanta had its systems ransomed for $51,000, did not respond to attackers’ demands fast enough, and will ultimately spend more than $11.5 million to recover from the data loss.
Attacks also continue to target older vulnerabilities. When my team reaches out to you about a newly discovered critical zero-day vulnerability, it’s imperative that you act quickly to patch your systems. But it’s also important that you have an effective patch management strategy that ensures that all security related patches get applied within a reasonable amount of time. The data shows that most breaches take advantage of vulnerabilities that are over 12 months old and have patches readily available when the breach occurs.
Since 2005, over 1.1 billion records have been breached in the US alone. There are only 300 million people in the US so most people have had their data exposed multiple times already. Based on the latest data available, there are approximately 17.6 million identity thefts a year, which results in around $15.4 billion in actual damages. To put these numbers in perspective, the total annual box office revenue for the US movie industry is only about $10 billion.
At Emory, the most common threat comes from bad actors trying to phish our users. It used to be simply user IDs and passwords these actors were after, but now that Duo is in place we see more instances of bad actors trying to trick our employees into providing them with sensitive information or to transfer funds into accounts controlled by the fraudsters.
Emory’s Enterprise Security infrastructure identifies and quarantines about 1,000 unique attackers a month and blocks over 200 million malicious communications each month.
In this hostile environment, Emory has much sensitive data that we need to protect.
Why Emory Cares About Data Security
 One reason Emory cares about protecting our data is because it is the law. HIPAA, FERPA, PCI, FISMA, etc. all require Emory to appropriately safeguard the data subject to these regulations (patient data, non-directory student data, credit/debit cardholder data, etc.). Additionally, when sensitive data is compromised, the financial impact can be extreme. Damages can easily be in excess of a million dollars, and all costs from such an incident are allocated to the individual school or division responsible for the incident, not by some central administrative unit.
One reason Emory cares about protecting our data is because it is the law. HIPAA, FERPA, PCI, FISMA, etc. all require Emory to appropriately safeguard the data subject to these regulations (patient data, non-directory student data, credit/debit cardholder data, etc.). Additionally, when sensitive data is compromised, the financial impact can be extreme. Damages can easily be in excess of a million dollars, and all costs from such an incident are allocated to the individual school or division responsible for the incident, not by some central administrative unit.
Data Breaches also damage the reputation of the institution. They negatively impact development and alumni relations activities, and can also affect Emory’s ability to get grants and contacts, and to attract the best and brightest faculty, staff, and students.
This risk is actively tracked and managed as part of Emory’s Enterprise Risk Management program, so it has visibility at the highest levels of executive leadership within the institution.
Why YOU Should Care About Privacy
You may be asking the question, “Why should I care on an individual level?” One reason, is that there can be legal consequences if you misuse sensitive information, including severe criminal penalties and fines.
In terms of identity theft and financial fraud, if your machine gets compromised, you are not only the one most likely to be victimized by identity theft as a result, your personal reputation is also at risk. In the event of a data breach, resulting from a compromise of your system, the leader of your business unit will be required to sign a breach notification letter that will be mailed to everyone who was affected by the breach. You don’t want to be the person who causes your executive leader to have to send an apology letter to 70,000 people.
Additionally, you could be subject to the loss or corruption of your data or be asked to pay a large ransom in order to get your data back.
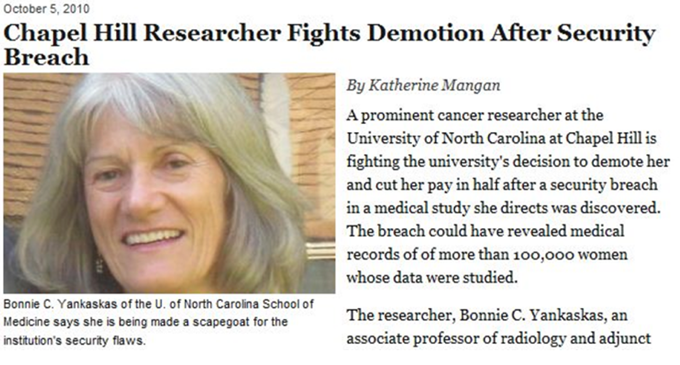 In 2010, a Chapel Hill researcher experienced a data breach on a project. The university demoted her and lowered her salary by half. She decided to sue UNC and they agreed to restore her position and salary so long as she immediately retired. While she regained some of her retirement benefits, she still had over $100,000 in unpaid legal fees and her career was over.
In 2010, a Chapel Hill researcher experienced a data breach on a project. The university demoted her and lowered her salary by half. She decided to sue UNC and they agreed to restore her position and salary so long as she immediately retired. While she regained some of her retirement benefits, she still had over $100,000 in unpaid legal fees and her career was over.
Preventing Data Breaches
What can you do to prevent these terrible things?
The first thing I tell everyone is to work with their local IT support for help securing their sensitive data. I also tell folks to eliminate or minimize the use of social security numbers whenever they can, and to move sensitive data to secure central storage locations. Don’t store this data on local devices like your desktop or laptop computer, smart phone, tablet, or USB drive, and in the rare event when this is unavoidable, be absolutely certain that any device used to store such data is encrypted.
It is also important to tightly control access to your data, ensure data transfer agreements are in place before transferring data to other institutions, and to delete old files that are no longer needed.
 In terms of your laptop or smart devices or removable media containing sensitive information, you should physically secure these devices whenever they are not under your direct control (with cable locks, or by locking them out of sight in a filing cabinet, for example). Never leave them unsecured or unattended, and especially never leave them unattended in your car. When a device like this is stolen the financial impact is way more than the replacement cost of the device, with the potential cost of a data breach easily running into the millions of dollars.
In terms of your laptop or smart devices or removable media containing sensitive information, you should physically secure these devices whenever they are not under your direct control (with cable locks, or by locking them out of sight in a filing cabinet, for example). Never leave them unsecured or unattended, and especially never leave them unattended in your car. When a device like this is stolen the financial impact is way more than the replacement cost of the device, with the potential cost of a data breach easily running into the millions of dollars.
You should also exercise good password management: choose a strong password, never share it with anyone, change it periodically, and always log out or lock your workstation before leaving it unattended. Also be sure to properly dispose of paper and electronic media that contain sensitive data. Paper records should be shredded and all forms of electronic media (CDs, DVDs, USB drives, Hard drives, Backup tapes, etc.) should be given to your local IT support staff who will securely store the devices until they are picked up and securely disposed of by Emory’s electronic waste disposal vendor.
Also try not to use email for communicating sensitive information if you can avoid it, especially if you need to communicate with people outside of Emory. Think of email like a postcard. Once the message leaves Emory you can be sure who might be able to read it besides the intended recipient, unless you encrypt it. To encrypt an email using Emory’s Office 365 email, add either (encrypt) or (secure), including the parenthesis to the subject line of your message and the message will be encrypted to any external recipients.
 It is also very important that you do not store sensitive data on unapproved cloud services like Google Docs, DropBox, Carbonite, iDrive, iCloud, etc. Emory’s Box and One Drive implementations are approved services for storing and sharing such data, so use one of these instead. Emory also has a suite of other applications and cloud services that have already been vetted for use with sensitive data. To find this list, simply search for “LITS Reviewed Apps” on the Emory home page.
It is also very important that you do not store sensitive data on unapproved cloud services like Google Docs, DropBox, Carbonite, iDrive, iCloud, etc. Emory’s Box and One Drive implementations are approved services for storing and sharing such data, so use one of these instead. Emory also has a suite of other applications and cloud services that have already been vetted for use with sensitive data. To find this list, simply search for “LITS Reviewed Apps” on the Emory home page.
For anyone who manages your own system(s), enabling and reviewing audit logs for your systems will help detect any potential misuse of your system and aid in the investigation of any anomalies, should they occur.
What else can you do?
- keep your system and applications up to date with all patches and anti-virus updates
- complete all required security and privacy training
- request a security scan or security review of your systems via ServiceNow
- understand your obligations (policies, regulations, grant and contract requirements) and comply with them
If you need any more information, please reach out to me or to the IT Security team at SecurityTeam-L [at] listserv [dot] emory [dot] edu.
Leave a Reply